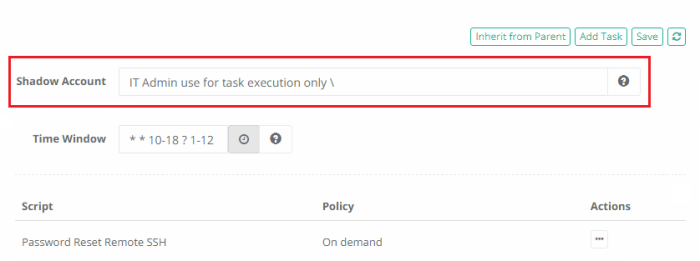
Shadow Account
A Shadow Account is a secondary account used to connect to the remote computer on behalf of the primary record account to perform the designated tasks.
Shadow Accounts cannot be used to rotate SSH keys.
A common scenario is that a user cannot reset a password however the Admin or root account can so that will be used instead.
Normally the record account is used to connect to the remote computer to execute scripts.
When a Shadow Account is specified for the task the script is executed under the Shadow Account privileges although it still has access to the main record account.
Cross-vault shadow account usage is not allowed. This means if you have a task running on a record in Vault A, it cannot be configured to use a Shadow Account record from Vault B.
The reason for this restriction is to prevent users from creating tasks in the place they can create them (personal vaults or vaults they can create records) to reset passwords that could be executed using powerful domain or root shadow accounts these users otherwise could not use.
You can modify the cross-vault blocker by adding/updating the following line to your $PAM_HOME/web/conf/catalina.properties file and then restarting the pam management service:
xtam.shadow.crossvault.disable=true #default is true
For example, you configure a Windows Host record with the user ituser@company.com to use in order establish secure remote sessions; however ituser@company.com does not have full permissions on the remote host to execute specific commands.
In this situation, when you would use this account to execute your tasks they would ultimately end up failing due to lack of permissions, but this is where Shadow Accounts can help.
You can leave the limited user ituser@company.com as the primary record account used for session connectivity and add a second Shadow Account itadmin@company.com which does have permissions to execute scripts on the remote host.
This gives you the ability to control the amount of permissions granted during a remote session while not limiting your ability to execute tasks and scripts with the proper permissions.
Shadow Account can be added directly to Record Types (i.e. Windows Host) so that they inherit down to all Records created from them or they can be added directly to Records that have unique Tasks configured.
Shadow Account used to execute the associated Script: