Integration with Okta SSO
If you are implementing or currently an Okta user, then the following article describes how to integrate the PAM login with Okta SSO.
This SAML integration currently supports the following features:
- SP-initiated SSO
- IdP-initiated SSO
Before you begin, be sure you met the following pre-requisities.
Pre-requisities
- A working PAM deployment with the Federated Sign-In experience.
- Access to the PAM host server to make application changes.
- An Okta Administrator account that can add Applications and basic Okta Administrative knowledge.
- PAM does not support the use of native Okta accounts for login. Accounts have to originate in Active Directory and be synced to Okta in order to be used for PAM authentication.
Add to Okta Application
This section will describe how to add the PAM Application in your company’s Okta tenant.
- Login to Okta with an Administrator account.
- Navigate to the Applications section and click the Browse App Catalog.
- In the Search for an application box, enter Imprivata Priveleged Access Managment. Click the Add button next to the application name.
-
In "General Settings" click Done.
Configuring PAM for your Okta SSO
This section will describe how to configure PAM to support your Okta SSO login.
We will be taking information from your PAM Okta Application and using them in the PAM configuration, so be sure you have access to both.
-
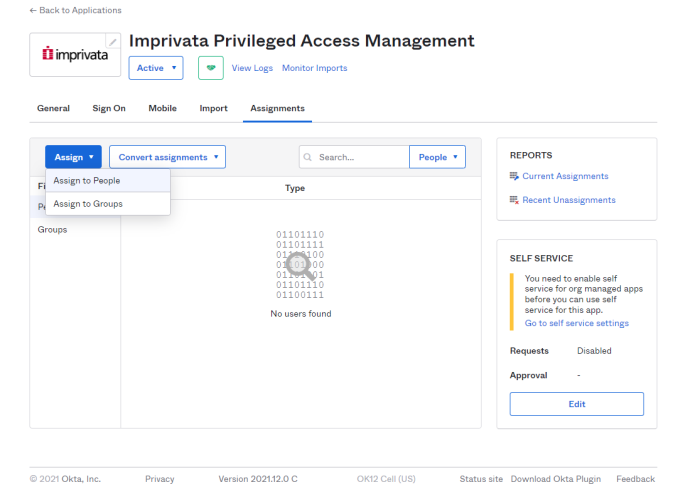
In tab "Assignments" assign rights to users. Click Assign and choice peoples or groups.
-
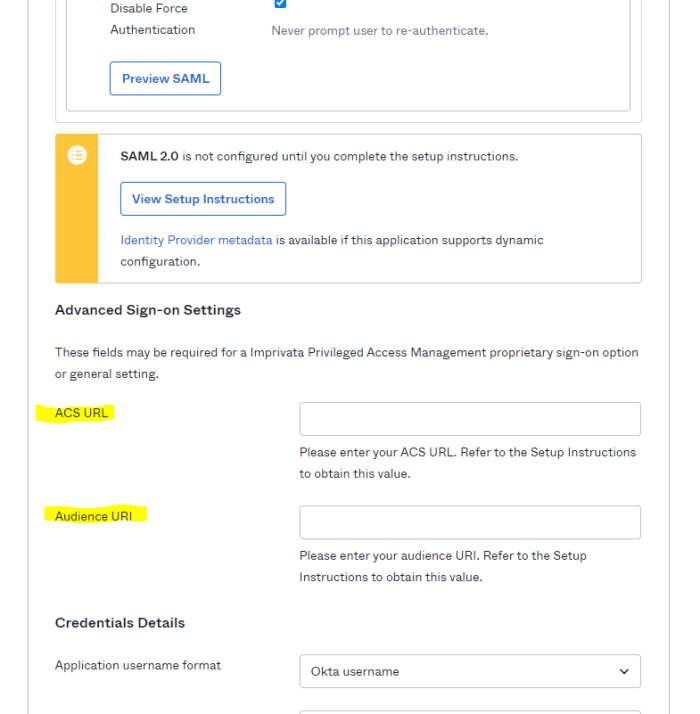
In tab "Sign On" press "Edit" in section "Advanced Sign-on Settings" enter your ACS URL and Audience URI values into the corresponding fields.
- ACS URL - <URL to your host>/cas/login?client_name=<SSO provider>,
- Audience URI - unique identificator, ex. urn:mace:saml:pac4j.org
ex. https://pam.company.com:6443/cas/login?client_name=Okta
-
End pressing Save.
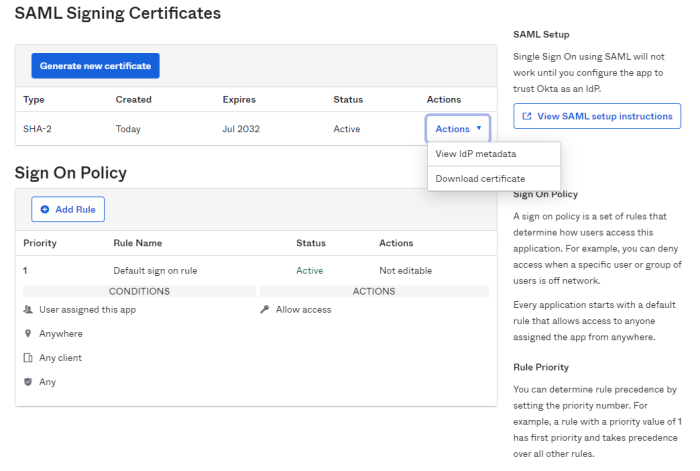
- In point SAML Signing Certificates click Actions, choose View IdP metadate and copy the opened URL.
- On the PAM host computer, open the following file in a text editor $PAM_HOME/web/conf/catalina.properties locate the section labeled # CAS and add the following lines:
- cas.authn.pac4j.saml[0].clientName=Okta - name SSO provider, it must match with item 2a.
- cas.authn.pac4j.saml[0].keystorePassword={testPassword} - Create an alphanumeric password. Any value you want to enter.
- cas.authn.pac4j.saml[0].privateKeyPassword={privatePassword} - Create an alphanumeric password. Any value you want to enter.
- cas.authn.pac4j.saml[0].serviceProviderEntityId={urn:mace:saml:pac4j.org} - audience URI, it must match with item 2b.
- cas.authn.pac4j.saml[0].serviceProviderMetadataPath={okta.xml} - The full path and file name of the okta.xml file. For example, $PAM_HOME/content/keys/okta.xml (use forward slashes not backslashes)
- cas.authn.pac4j.saml[0].keystorePath={samlKeystoreOkta.jks} - Define a path and name for the PAM auto-generated key. For example, $PAM_HOME/content/keys/samlKeystoreOkta.jks (use forward slashes not backslashes)
- cas.authn.pac4j.saml[0].identityProviderMetadataPath={path} - Copy and paste the full URL from your Identity Provider Metadata used in step (4). For example, https://subDomain.okta.com/app/[externalKey]/sso/saml/metadata.
- cas.authn.pac4j.saml[0].maximumAuthenticationLifetime=2073600: This value defines a 24 day period (value in seconds) in which a user has generated a last authentication event in Active Directory. This parameter helps if users begin experiencing login issues due to old authentication events.
-
When finished, save and close this file.
-
Restart the PamManagement (Windows) or the pammanager (Linux) service.
-
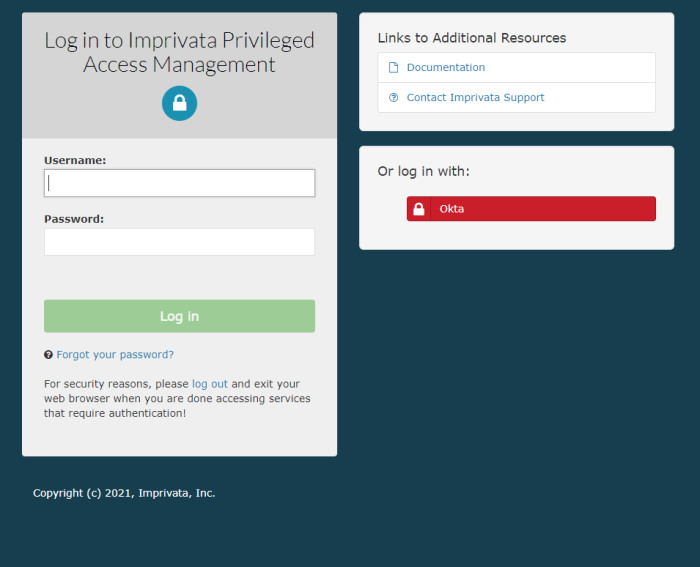
When the service is fully restarted, open your browser and navigate to the PAM login page. Use the new option Login using Okta located on the bottom right side of the page.
cas.authn.pac4j.saml[0].clientName=Okta
cas.authn.pac4j.saml[0].keystorePassword={password}
cas.authn.pac4j.saml[0].privateKeyPassword={password}
cas.authn.pac4j.saml[0].serviceProviderEntityId=urn:mace:saml:pac4j.org
cas.authn.pac4j.saml[0].serviceProviderMetadataPath={okta.xml}
cas.authn.pac4j.saml[0].keystorePath={samlKeystoreOkta.jks}
cas.authn.pac4j.saml[0].identityProviderMetadataPath={path}
cas.authn.pac4j.saml[0].maximumAuthenticationLifetime=2073600
In the lines above, the following {placeholders} need to be updated using your own values explained here.
Save and close the file when you are finished.
Please note, if you made changes around SSO parameters to the $PAM_HOME/web/conf/catalina.properties file with the previously generated .xml and .jks files, you need to regenerate those files to apply the new changes.
To regenerate .xml and .jks files
-
On the PAM host computer, open the following file in a text editor $PAM_HOME/web/conf/catalina.properties locate the section labeled # CAS and specify the stated location for those files.
-
Remove or delete these previously generated .xml and .jks files from the location.
-
Restart PamManagement (Windows) / pammanager (Linux/Unix) service to regenerate those two .xml and .jks files, so your changes around SSO parameters can apply back to PAM.