OpenLDAP Complaint Server Password Change
The following page describes the configuration process to automate the password reset or rotation of user and administrator accounts from an OpenLDAP compliant server.
- Login to PAM with a System Administrator account.
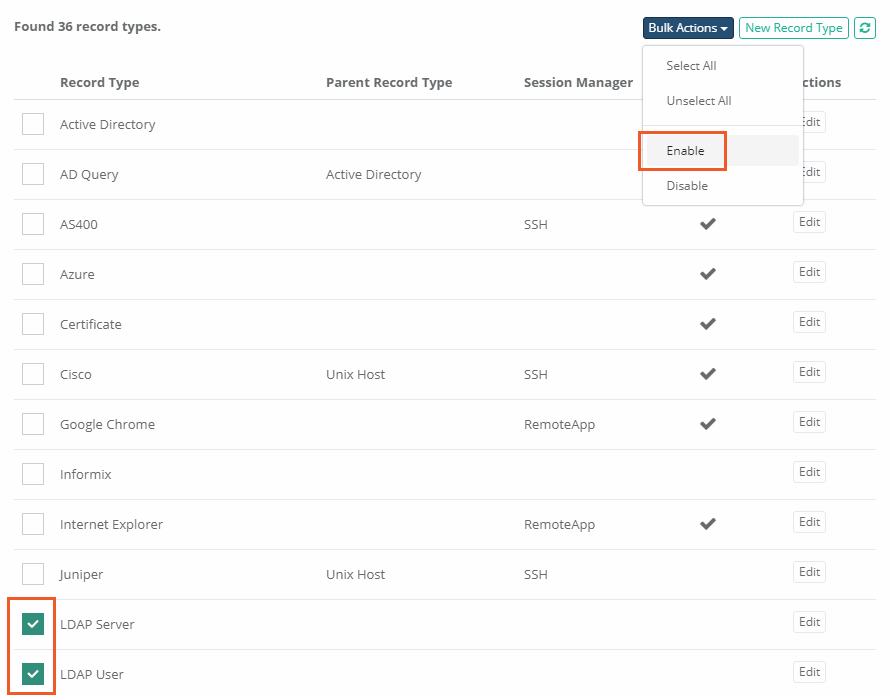
- Navigate to Administration > Records Types.
- Locate and select the Record Types LDAP Server and LDAP User, then click the Bulk Actions dropdown and choose Enable. This will make both Record Types available to be used as Records in PAM.
-
Now that the Record Types are enabled, we will first create a new LDAP Server record. Navigate to your PAM Record List location and select LDAP Server from the Add Record dropdown menu.
-
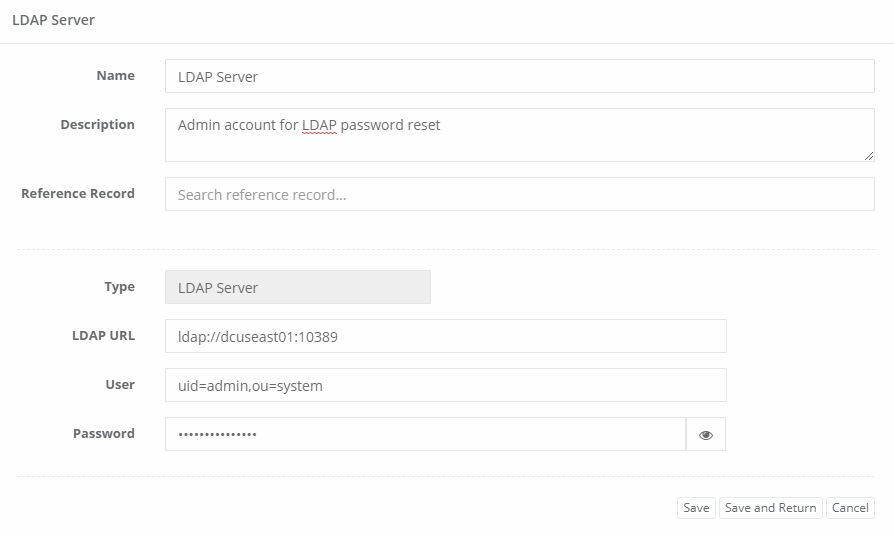
For this new LDAP Server record, enter the URL to your LDAP server, the LDAP Administrator DN and this Administrator’s Password. For example:
-
LDAP URL:ldap://dcuseast01:10389
-
User:uid=admin,ou=system
-
Password:Adm1nPass@word1
-
-
Click Save and Return when finished.
-
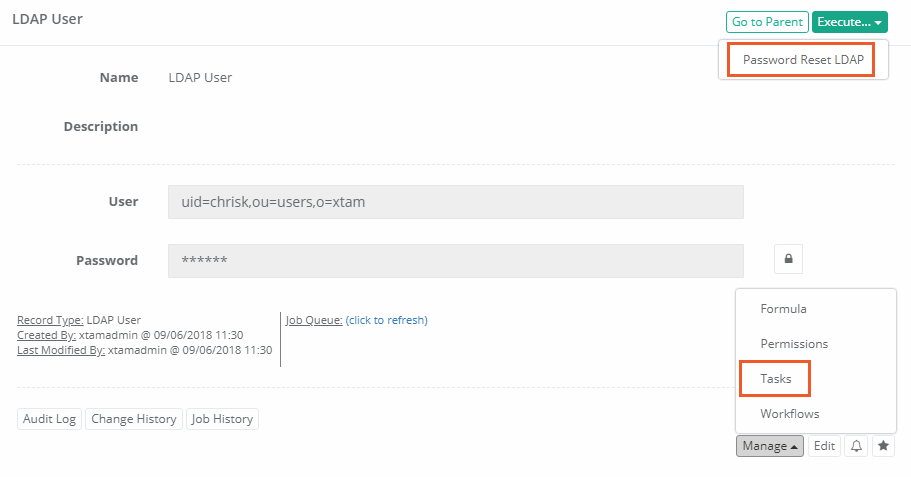
Navigate back to Administration > Record Types and click the Edit button next to the LDAP User record type.
-
Within the LDAP User record type configuration, click the Tasks button.
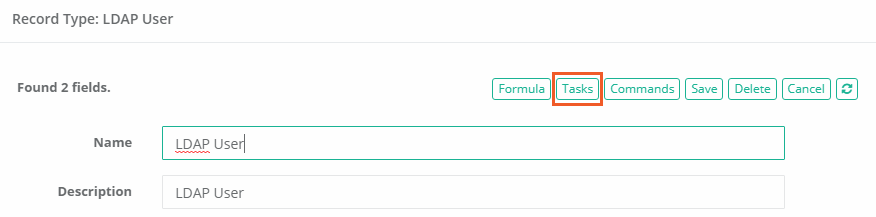
You can also customize the password complexity policy by clicking the Formula button on this page.
-
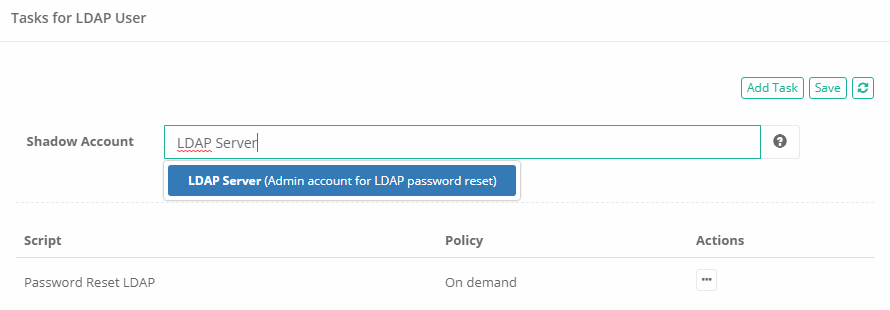
Now we will make our LDAP Server record as the Shadow Account for this task. In the Shadow Account field, enter the name of the LDAP Server record that was created in a previous step.
By associating the LDAP Server record as a Shadow Account for the LDAP User record type, this configures PAM to use the User and Password for the Server to execute the Password Reset task for all the LDAP User records.
-
Click Save when finished.
-
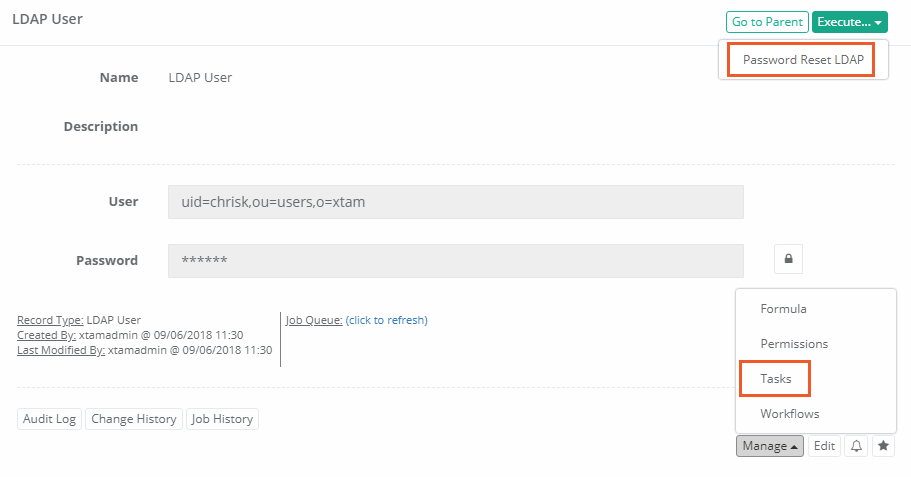
Return to your PAM Record List and create a new LDAP User record. This record will contain the user account whose password will be reset or automatically rotated.
-
Enter the values in the LDAP User record as needed. For example:
-
User:uid=chrisk,ou=users,o=xtam
-
Password:usersPassword
-
-
Click Save and Return when finished.
-
When the record is saved, you may now configure the Tasks on this record for automatic password reset or you can manually execute the Password Reset task to reset it now.
An Administrator account is required for this record because it will be used as a Shadow Account to reset the passwords of other non-Administrative user accounts.
Please note that this process assumes the password for users is stored in the directory attribute userPassword. If this is not the case in your directory, then you will need to add a new field to the LDAP Server content type with the following values:
Field Type: String
Name: PasswordAttribute
Display Name: Password Attribute
Then when creating this LDAP Server record, you should specify the name of your directory attribute that stores passwords in the PAM record’s PasswordAttribute field.
This same configuration can be used to reset an Administrator’s account password with the exception that a Shadow Account is not needed because these accounts can reset passwords without requiring elevated permissions. You would only need to create and use the LDAP Server record to reset that Administrator's account password.