SSH Key Management
SSH Key Management and Automated Rotation.
With increasing popularity of Unix and Linux systems in the enterprise space, it is becoming a growing concern to Security personnel as they are not typically accessed like a Windows-based server.
In many instances, Unix and Linux endpoints are secured not with a traditional username and password, but rather they are accessed via SSH using a private/public keypair. And much to the disapproval of Security professionals, these keys can sometimes be made to work across multiple servers and are rarely, if ever, updated. This means if a threat gains access to one of your SSH keys, they can potentially access areas of your enterprise infrastructure without warning or consent.
With Imprivata Privileged Access Management software, one can easily and safely store any number of SSH keys with the additional benefit of secure sharing with others, auditing usage of the keys and providing remote access to these Unix endpoints without giving user’s the key itself.
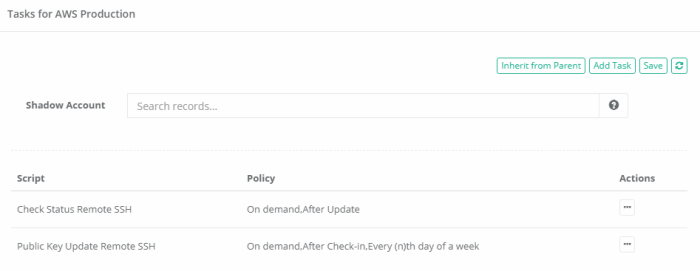
Even if the key itself is never shared with another human again, PAM also provides the ability to automatically rotate the SSH key based on configured policies (scheduled or on-demand), ensuring no one can ever again gain access without your knowledge or approval.
To begin implementing SSH Key Management in your PAM deployment today, simply create a record using either the Unix Host with Key or Unix Host with Protected Key record types (or create your own custom record type using the File field) and save your key into PAM’s secured Identity Vault.
Next, configure your Public Key Update Remote SSH rotation policy and finally share access to it with your authorized users.
For your SSH keys, PAM will:
- Safely store your SSH key(s) in a centralized location.
- Prevent unauthorized access to both them and the corresponding endpoint.
- Automatically rotate the key(s) based on a schedule or on-demand.
- Provide an easy means to share access to the key with employees and outside contractors, but not the key itself.
- Audit, report and alert all interactions and activities associated with the key.
- Generate Request and Approval Workflows so Senior level or Managers can grant access to these keys.
- Establish a recorded remote SSH session (client or browser) to this protected endpoint.